BSidesPGH 2018
Conference Friday June 23rd at Rivers Casino.
Training Thursday June 22nd at Left Field Meeting Space.
Track Gold
Track Black
9:00
REST is the Sweet Sauce of Labor
Kevin Cody
10:30
SOC Them in the Face: Building and Attacking SOCs
Eric Carroll, Andrew Johnston
11:10
Wormholes: Fact, not (Science) Fiction
Aaron Shelmire, Christian Roylo
Java Serialization: The Serial Killer
Robert C. Seacord
12:00 Lunch
1:30
Heavy Machinery and Burly Lumberjacks and Logging! Oh My!
Dan Astor, Evan Perotti
RMF in a DevOps World!
aka "He’s dead Jim!”
Scott Zimmerman, Frank Cameron, Lucas Truax
2:30
No Disassembly Required
Nate Guagenti, Brian Satira
It’s Not You; Job Searching is Broken
Erik Ligda, Deidre Diamond
3:30
Fileless Malware
Jim VanDeRyt
5:00 Closing Remarks & Happy Hour featuring Selecta
Title: Data Wrangling Lessons from the OWASP Top 10
Abstract: The goal of the OWASP Top 10 project is to raise awareness and create a baseline for application security by identifying some of the most critical risks facing organizations. The Top 10 project is referenced by many standards, books, tools, and organizations, including MITRE, PCI DSS, DISA, FTC, and many more. To shape the OWASP Top 10 2017, the project ran a public call for data and industry survey to help define what should be included in the list.
Gain insight into some of the details of the OWASP Top 10 Call for Data and industry survey, and what we were attempting to learn. Hear about was learned from collecting and analyzing widely varying industry data and attempts to build a dataset for comparison and analysis. This talk will discuss tips and common pitfalls for structuring vulnerability data and the subsequent analysis. Learn what the data can tell us and what questions are still left unanswered. Uncover some of the differences in collecting metrics in different stages of the software lifecycle and recommendations for handling them.
Bio: Brian Glas has worked in IT for over 17 years and information/application security for the last decade. He started as an enterprise Java developer, then transitioned to helping build an application security program as both tech lead and manager. He later played the role of enterprise architect and did a little incident response and reverse engineering malware for fun. Glas then spent a number of years as a consultant helping clients build AppSec programs, create/update SDLCs, and other related initiatives. He has worked on the Trustworthy Computing team at Microsoft and is currently working at nVisium as the Director of Strategic Services. He was a co-lead for SAMM v1.1-2.0 and the OWASP Top 10.
Title: REST is the sweet sauce of labor.
Abstract: Contrary to Plutarch's famous quote regarding rest being the "sweet sauce" of labor, RESTful web services may actually be the *source* of additional security labor. A service or microservice architecture demands a different sort of security testing knowledge base, tooling, and perspective. Tools such as Swagger, Postman, and Insomnia can help your testing efforts; however, a basic understanding and security foundation is critical in getting the most out of your time invested in these tools. Attendees will learn useful nomenclature, tutorials, and expertise that will be benefit anyone dealing with risk assessments, vulnerability analysis, or penetration testing of RESTful web services.
Bio: Kevin Cody is a Principal Application Security Consultant with experience working at several Fortune 500 enterprises. Although his particular expertise is geared toward hacking Web and Mobile applications, he is also experienced in the entire gamut from mainframes to embedded systems. Kevin is adamant on helping build-up developers through security, which can be seen in his involvement within OWASP or while speaking at events like CodeMash or BSides. In his spare time, Kevin can be found attempting to repair something (via online DIY videos), reading tech books, fishing, or simply spending time with his wife and children.
Title: Sentry or: How I Learned to Stop Worrying and Delete My Accounts
Abstract: With social media, anyone can become "incidentally infamous" in minutes. Your tweet could go viral, your gif could get posted by a president, or the media could single you out because they think you made Bitcoin. This happens to hackers too, @MalwareTechBlog was arrested after DEF CON 2017 and certain media started doxing him and painting him as a spendthrift criminal based on his Twitter posts. Rather than become a social media hermit to prevent this, just set up a Sentry. This talk will present Sentry, an automated cross-platform application that will silently watch your social media for trigger words and unusual behaviors before springing into action. In minutes Sentry can lock your Twitter account, delete your Reddit comments, disable your websites, and a whole host of other actions to keep attention away in high visibility, low-privacy situations. Released under the MIT license and easily extensible, virtually any site and any API can be scripted with a bit of C#.
Bio: Michael West, aka T3h Ub3r K1tten, is a Technical Advisor at CyberArk who likes cats and is addicted to Twitter. His homelab has over 640 kilobytes of RAM. Michael presents regularly at Dallas Hackers Association and enjoys combining his software dev background with infosec to build tools for others. His interests include OSINT, amateur radio, and scanning long barcodes on the beach.
Title: SOC them in the face: Building and Attacking SOCs
Abstract: The goal of any attacker or red teamer is generally to avoid the employees of the Security Operations Center (SOC), as they are primarily responsible for detecting and remediating threats to the
network. However, what happens when the attackers start targeting the employees of the SOC itself? In this presentation, we combine our experiences in building and attacking SOCs to demonstrate how
attackers can target the employees and structure of the SOC to evade detection. We finish the presentation by providing some best practices on building, training, and utilizing a SOC to ensure it remains effective against today’s advanced attacks.
Bio: Eric Carroll is a Strategic Consultant at Mandiant, a FireEye Company. As part of the Strategic Security Consulting team, Mr. Carroll supports consulting services across security program development, security assessments, security monitoring and response capability development, technical and executive-level tabletop exercises. Mr. Carroll has worked with multiple Fortune 500 companies in nearly every industry, helping to assess and mature their Cybersecurity programs. Eric holds a bachelor’s degree from Indiana University of Pennsylvania (IUP) in Computer Science and a master’s degree in Information Security and Assurance from Robert Morris University (RMU).
Bio: Andrew Johnston is a Proactive Consultant at Mandiant, a FireEye Company. His work focuses on gaining access to critical buildings and systems through covert tactics. Andrew also is the lead researcher of a team at Fordham University focused on using artificial intelligence to solve problems in the counter-terrorism, narcotics trafficking, and national defense sphere. He holds a bachelor's degree from Fordham University with a dual major in computer science and applied mathematics and is currently pursuing a master’s degree in Cybersecurity. This is his first time at BSides Pittsburgh and his third
BSides presentation.
Title: Wormholes: Fact, not (Science) Fiction
Abstract: During 2017 news reports were dominated by three worm events, largely due to the worms’ use of exploits originating from the NSA, the suspected nation state origin of the attacks, and the destructive payloads they delivered. This presentation covers the observed impacts of WannaCry, NotPetya, and BadRabbit at organizations; what really happened which led to the spread (or non-spread) of these worms; a fourth worm event that impacted many more organizations but received less press-coverage; and the defensive measures freely available to everyone to mitigate these attacks.
Bio: Aaron Shelmire wove a long path in security research starting at the Pittsburgh Supercomputing Center, meandering through Carnegie Mellon’s Heinz School at night towards a gig at CERT/CC and an adjunct position at CMU, before jumping to the private sector to work in established organizations and startups over the past 5 years, currently working at Secureworks.
Bio: Christian Roylo is a Senior Information Security Consultant with the Special Ops Team of Secureworks Counter Threat Unit. He has a total of 25 years of investigative and computer security experience with various organizations including the US Secret Service, Software Engineering Institute at Carnegie Mellon, and the last 4 years with Secureworks as a threat hunter.
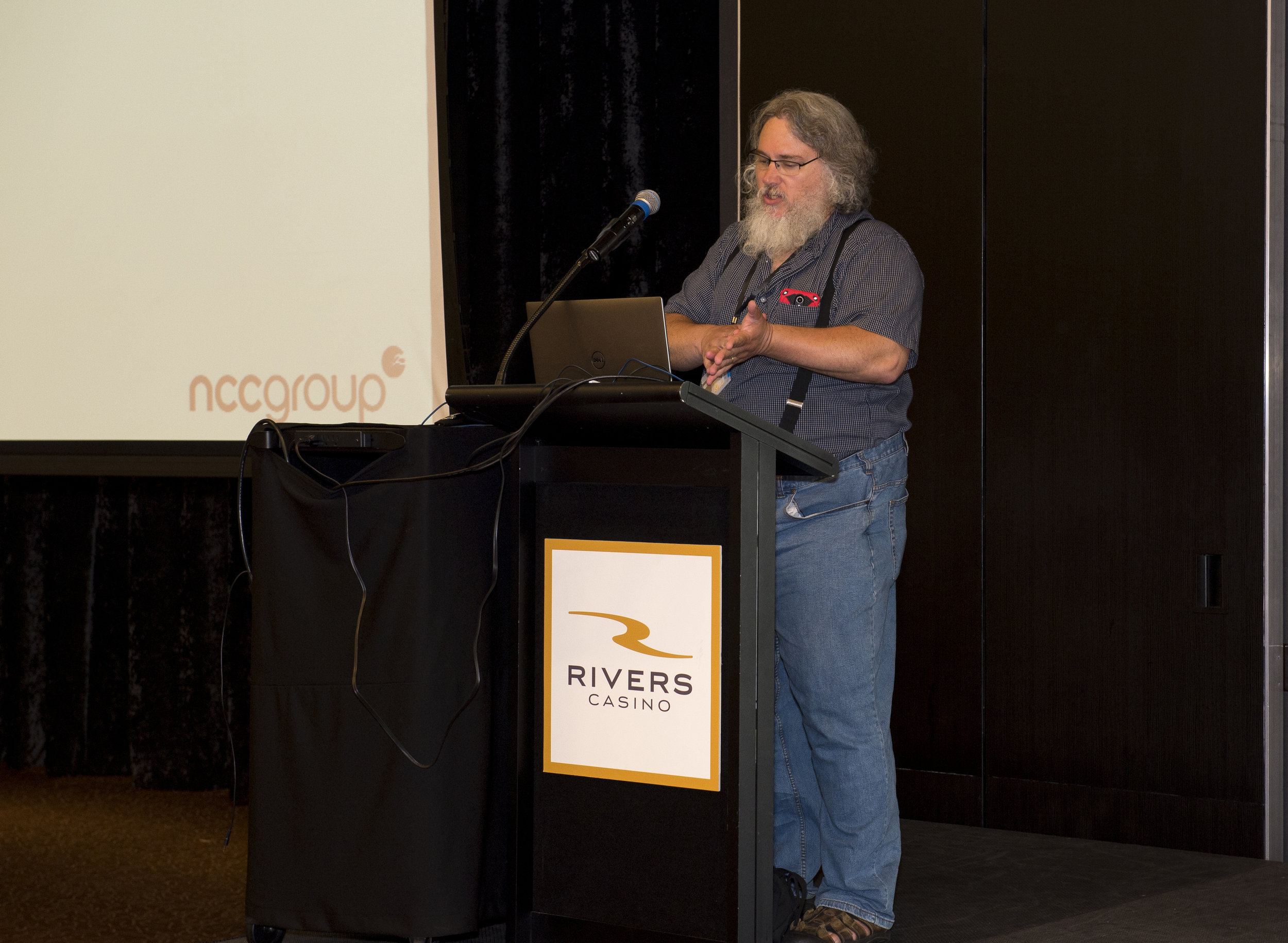
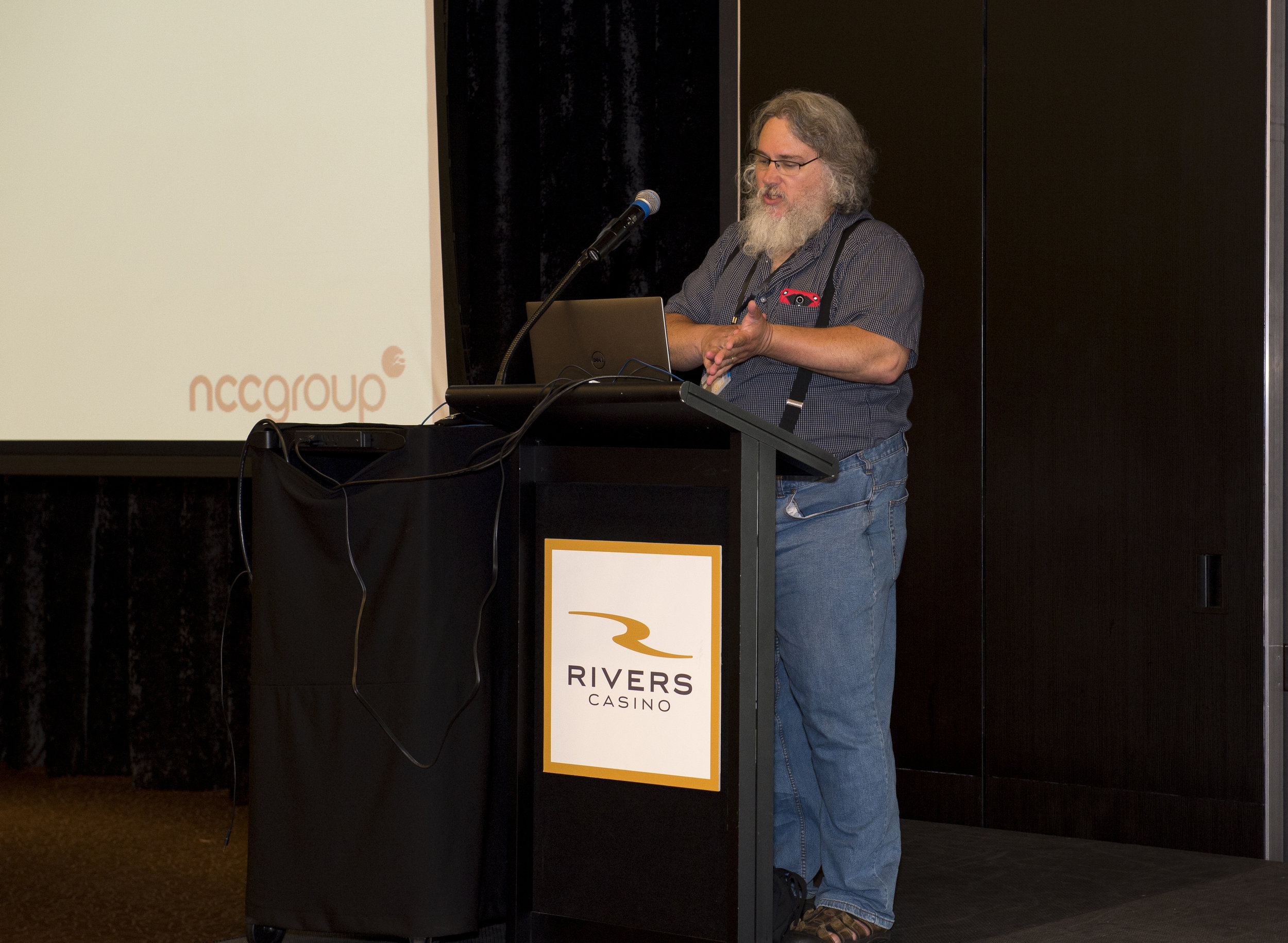
Title: Java Serialization: The Serial Killer
Abstract: This presentation provides developers with practical guidance for securely implementing Java Serialization. Java deserialization is an insecure language feature included in the OWASP Top 10 Application Security Risks – 2017. Serialization is widely used both directly by applications and indirectly by Java subsystems such as RMI (Remote Method Invocation), JMX (Java Management Extension), JMS (Java Messaging System).
The presentation will demonstrate how deserialization of untrusted streams can result in remote code execution (RCE), denial-of-service (DoS), and a range of other exploits. Applications can be vulnerable to these attacks even when no coding defects are present. This webinar explains and demonstrate these attacks and show developers how to securely code their systems to support Java serialization.
In particular, participants will learn:
· How Java serialization/deserialization works
· How to determine if your systems are vulnerable to Java deserialization exploits
· How to use serialization filtering in Java 10 to mitigate vulnerabilities
Bio: Robert C. Seacord (@RCS) is a Technical Director at NCC Group and works with software developers and software development organizations to eliminate vulnerabilities resulting from coding errors before they are deployed. Robert is a renowned computer scientist and author, known as the “father of secure coding.”
Previously, Seacord led the secure coding initiative in the CERT Division of Carnegie Mellon University’s Software Engineering Institute (SEI). Seacord is also an adjunct professor in the School of Computer Science and the Information Networking Institute at Carnegie Mellon University. Seacord is the author of six books, including The CERT C Coding Standard, Second Edition (Addison-Wesley, 2014) Secure Coding in C and C++, Second Edition (Addison-Wesley, 2013), and Java Coding Guidelines: 75 Recommendations for Reliable and Secure Programs (Addison-Wesley, 2014). Seacord is on the Advisory Board for the Linux Foundation and an expert on the ISO/IEC JTC1/SC22/WG14 international standardization working group for the C programming language.
Title: Heavy Machinery and Burly Lumberjacks and Logging! Oh My!
Abstract: Did we get the creds? Do we have a beacon? Are we burned? All questions that get asked during a red team engagement with high frequency. With a full red team infrastructure, you need to manage a mini-network to be successful. Cobbling together monitoring scripts, tailing files, or grepping for tokens to see if payloads were downloaded or if phishing credentials were entered can be painful and inefficient when you could instead be planning your next move or taking advantage of a successful compromise.
We need some way to organize all these logs and data into a centralized location that can alert us when important events happen. Perhaps a SIEM... By ingesting logs from all our hosts used during an engagement, we can begin to visualize our network of attack machines and create alerts for priority events like phishing credentials being submitted, IR teams and security vendors hitting your server, and changes in server health. This talk will cover the ins and outs of why to use a SIEM for your red team infrastructure, the free products out there that can assist, and how we went down the path of using Elastic for our Red SIEM. We'll also be releasing our tools, scripts, and resources to aid you in deploying and monitoring your own Red SIEM.
Bio: Dan Astor – Dan is a senior operator for Security Risk Advisors’ Technical Assessment team. His focus is in red team operations, network penetration testing, password cracking, and spear phishing. He has been a speaker at BSides PGH and BSides NOLA.
Bio: Evan Perotti – Evan is an operator for Security Risk Advisors’ Technical Assessment team. His focus is in red team operations, network penetration testing, reconnaissance activities, and spear phishing. He has developed a number of open source and private tools to automate common offensive activities.
Title: RMF in a DevOps World! aka "He’s dead Jim!”
Abstract: The threats posed to software applications and information systems are constantly changing. In order to address the shifting landscape and help keep information systems in a continual state of protection, the federal government introduced the Risk Management Framework (RMF). RMF is a six-step, process focused on better securing networks and information systems by introducing the concepts of continuous system security via constant monitoring, assessing, and testing of controls. It was developed to replace the previous federal certification and accreditation process that mainly focused on prescriptive security controls and assessing the security of systems at a single point in time. At the same time, the processes and concepts by which modern software is developed, integrated and delivered is also rapidly evolving. As the federal government was moving from a prescriptive-based approach to application of security controls, a cultural shift began to happen within the software development world defined as DevOps. The term DevOps is a portmanteau of the words, development and operations, and has come to represent the goal of increasing automation throughout the software design life cycle (SDLC). The goal of DevOps is to break down the traditional separation between these two organizational units, and to deploy changes in a rapid, iterative fashion. With DevOps, the development cycle is shortened and the size of code
release is smaller. The goal of rapid deployment may seems to run counter to the goal of security and the ability to ‘bake’ security in from the beginning.
Bio: Scott ZImmerman, CISSP, ISSEP, is a Principal Cyber Engineer and Chief Information Security Officer at Concurrent Technologies Corporation. He has over 25 years of cyber expertise working within DoD, Intelligence Community and commercial clients. He a experienced
public speaker and author. Mr. Zimmerman’s education includes a B.S in Management Information Systems.
Bio: Frank Cameron is a Senior Cybersecurity Engineer at CTC with over 15 years of experience in cybersecurity, software development, security automation and systems engineering. Mr. Cameron’s education
includes a B.S. in Computer Science. Mr. Cameron holds certifications as a Certified Ethical Hacker and a Certified OpenStack Admin.
Bio: Lucas Truax, CISSP, is a Senior Cybersecurity Engineer at CTC. He began in IT as a developer and has worked in IT security for most of the last decade both securing and attacking a variety of information systems. Mr. Truax’s education includes a B.S. in Management Information Systems and a M.S. in Software Engineering. Additionally, Mr. Truax holds the GIAC Response and Industrial Defense (GRID) and Certified Information Systems Security Professional (CISSP) certifications.
Title: No Disassembly Required
Abstract: Does malware analysis seem like an arcane process involving hours of staring at assembly in OllyDbg or IDA? Is the only alternative relying on an "auto-magically" generated report from a sandbox? Many of the malware variants that today's analyst will face during incident response are not compiled binaries like Windows PE files. We will demystify analysis of JavaScript and VBA/VBS trojan downloaders embedded in phishing email attachments, PowerShell scripts used for post-exploitation, and tiny web shell backdoors. Our talk will seek to familiarize frontline defenders and anyone interested in the state of “now” malware analysis, with modern script-based variants.
Bio: Nate Guagenti - Utility man who, in his short 5 yr career in infosec, has worked on everything from engineering a 40Gbps+ Bro solution to incident response to database/SIEM implementation+design. Nate has spoken previously at DerbyCon, BSides Detroit, BSides Columbus, and BloomCon.
Bio: "Brian Satira is a malware rodeo clown and accidental fuzzer. You can follow him @r3doubt on Twitter or at https://blog.r3doubt.io/"
Title: It’s Not You; Job Searching is Broken
Abstract: After spending 15 years in security at a mid-sized DoD contractor and starting a job search as a security architect, I thought finding a new job would be easy. After all, we are told that there are “more than 1M vacant cybersecurity jobs in the U.S.” My journey was far from easy; resume edits, pitfalls, miscommunication, and unclear job descriptions resulted in failed job search after failed job search. The job searching process forced me into communication with recruiters who didn’t speak security and resulted in interviews for any and all security positions, thus wasting everyone's time. The compilation of job searches created an abundance of self-doubt and not the shiny new opportunity for which I had been seeking.
Fast forward to today where I am the Cyber Security Architect for CyberSN, a cyber staffing firm. My confidence has been restored, and I have gained valuable insight into how the staffing process has been systemically broken for a long time. During our presentation, Deidre Diamond (CyberSN Founder and CEO) and I will share my story and provide first-hand examples of obstacles that led to a miserable job
search experience, a common theme among my peers in the security industry. We will offer insight as to how this breakdown occurred and how it could have been avoided. We will provide key information, tactics, and advice to self-market, evaluate recruiters, ace the interview, and successfully negotiate salary.
Bio: Erik Ligda is a Security Architect at CyberSN, a national cyber security research and staffing organization. At CyberSN, Erik’s responsibilities include the protection of the company’s intellectual
property and brand image. Additionally, Erik leads CyberSN’s contracting division, acting as a trusted resource for education, training, and career development.
Prior to joining CyberSN, Erik worked at Concurrent Technologies Corporation where he spent 15 years growing and leading the cyber security and incident response teams. Erik holds a Certified Information Systems Security Professional (CISSP) certification
and additional certifications as a GIAC Certified Intrusion Analyst, GIAC Certified Information Handler and GIAC Reverse Engineer.
Bio: Deidre Diamond is the CEO and Founder of CyberSN.com, a cyber security research and staffing company, and the Founder of brainbabe.org, a cyber security not-for-profit organization. Deidre’s vision and leadership has resulted in a dramatic decrease in the frustration, time and cost associated with job searching and hiring for cyber security professionals.
Prior to CyberSN, Deidre was the CEO of Percussion Software, the first VP of Sales at Rapid7 (NYSE:RPD) and the VP of Staffing and Recruiting for the national technical staffing company Motion Recruitment. Deidre leads with a strong commitment to transparency, equality, training, support, high-productivity and love in the workforce.
Title: Tactical, Practical Digital Forensics
Abstract: Digital forensics continues to change. Commercial forensic tool suites have evolved and offer many features. Endpoint Detection and Response (EDR) tools capable of cybersecurity monitoring, threat
detection and investigative response are becoming more and more popular. But, what if you don't have a digital forensics tool suite? What if an EDR solution is not an option?
The answer: 'Tactical, Practical Digital Forensics: The 12 Must-Have Tools'. Many open-source and free commercial digital forensics tools have kept up with the times too. These tools not only provide options for forensic investigators on a budget, but also perform well in getting the job done.
This tactical, practical digital forensics overview provides attendees with the tools and associated techniques to collect, preserve, parse, and analyze the key artifacts for resolving malware related data
breaches and cybersecurity incidents. These 12 must-have tools focus on the most relevant system files and data, are fast and easy to use, and provide easily reviewable outputs.
Bio: John Grim has over 15 years of experience investigating data breaches and cyber security incidents within the government and civilian security sectors. Currently, John serves as a part of the Verizon Threat Research Advisory Center (VTRAC) by leading a team of highly skilled digital forensics investigators. In this role, John leads a team of highly-skilled, digital investigators who respond to cybersecurity incidents, conduct on-site threat mitigation activities, and perform digital forensic examinations.
Prior to joining Verizon in 2009, John served 12 years with the U.S. Army investigating national security-related incidents. Throughout his over 20 years of experience fulfilling various security, intelligence, and investigative roles in the government and civilian security sectors, John has provided computer security related advice, assistance, and formalized instruction to both technical and non-technical audiences. John has also authored or contributed to various policies, procedures, processes, handbooks, and training materials on incident response, evidence handling, and forensic examinations.
Title: The Marriage of Threat Intelligence and Incident Response or... Threat Hunting for the Rest of Us
Abstract: Most organizations don't have a large security team, or the ability to conduct active threat hunting. This doesn't mean that we can't utilize the skills and information we have to conduct threat hunting techniques into our incident response process. This talk will focus on utilizing Open Source Intelligence (OSINT), open source tools, and incorporating this into not only our incident response process, but also conduct threat hunting operations.
Bio: For 20 years, Jamie Murdock has specialized defending, securing, and protecting corporate networks. During this time, he built security operation centers for Fortune 500 companies, providing expert guidance in all areas of security operations. He has built incident response and threat intelligence programs, focusing on profiling threats specific to individual organizations, and took this information and built adaptive monitoring programs.
Title: Red and Blue team Tips for Cryptocurrency Mining on Your Organization Infrastructure
Abstract: You’ve heard about malicious Cryptocurrency mining in the news but have you ever looked to investigate the potential for an insider to profit from Cryptocurrency mining within your organization? There exists a perception that cryptocurrency mining is difficult to setup and is simple to detect. With this talk I hope to provide the audience with evidence that it is extremely simple for an insider (employee) within the organization to take full advantage of the resources available to them all while going undetected. The presentation also details in full potential rates of return for hardware mining and costs which could be incurred for the organization. Along with the cost/return data, Red and Blue team tips will be provided as to better explain how each side works to optimize their processes. The talk will also include a PowerShell script for the audience which can be used to detect artifacts of known Cryptocurrency mining software if the user thinks their asset/s may have been used for such purposes.
Bio: Joe Mast is an Information Security analyst working for Federated Investors in Pittsburgh Pennsylvania. Throughout his first year he has worked on building a strong and broad foundation for cyber security in multiple domains including PowerShell, Cryptocurrency, and vulnerability management. Joe is very driven and currently working on his M.S. in Cybersecurity and Information Assurance and will be taking a SANS course this summer.
Title: Fileless Malware
Abstract: In 2017, over half of all malware was file-less malware. As cyber threat adversaries evolve, so do their methods. Today, file-less malware is more prevalent in organization's environment than file-based malware because file-based malware can be detected and blocked with current security controls due to the fact that file-based malware is detectable via artifacts known as Indicators Of Compromise. To resolve this dilemma, cyber threat adversaries had to find a way to complete their malicious operations without being detected by current controls. Since file-less malware leaves almost no artifacts, there can be no threat detection or threat hunt using Indicators Of Compromise because no IOCs exist. Instead, Tactics, Techniques and Procedures (TTPs) that cyber threat adversaries use are the way to detect modern attack scenarios.
Bio: Jim VanDeRyt has worked in information security for the past 17 years. Jim spent almost 7 years at Internet Security Systems where he learned network security such as intrusion prevention systems, vulnerability management and some host-based protection. Next, Jim spent 2 and half years with a reseller learning various security technologies such as data loss prevention, wireless planning and security, firewalls, network access control, host and file encryption, and some database security and application security. Prior to Cybereason, Jim was at Imperva for 4 and half years where he learned about securing structured business data which usually resides in databases and is usually accessed by web applications in most customer's environments today. After Imperva, Jim worked at Fidelis CyberSecurity for 3 and half years where he learned about advanced threat detection/prevention on the network.
Training
Title: Training 1 - Incident Response Evidence Collection / Triage
Trainer
John Meyers - Senior Incident Response Analyst, NTT Security
Abstract
Incident Response succeeds or fails at evidence collection. If you don't collect evidence properly or soon enough, you might not be able to determine the root cause of the incident. I will explain how and when to start your evidence collection process, verifying your evidence, hashing your evidence, and the concept of working copies to examine your evidence. The demonstration will include capturing disk image and device memory using FTK Imager.
Incident triage is the process reviewing gathered evidence in an expedient manner to answer important questions. Topics will include the usefulness of artifacts including Memory, Windows Registry, Browser History and Event Logs. Memory triage would cover basic usage of Volatility to find running processes, network connections and review other artifacts available in memory. Disk triage would cover locations of key artifacts including Registry, Browser History and Event Logs as well as tools to analyze these artifacts.
Title: Training 2 - No Disassembly Required
Trainers
Nate Guagenti - Utility Man, R3doubt
Brian Satira - Malware Analyst, R3doubt
Abstract
Does malware analysis seem like an arcane process involving hours of staring at assembly in OllyDbg or IDA? Is the only alternative relying on an "auto-magically" generated report from a sandbox? Many of the malware variants that today's analyst will face during incident response, however, are not compiled binaries like Windows PE files, and do not require a knowledge of assembly to manually analyze. The goal of our training is to equip frontline defenders with skills to begin more advanced analysis of common malware variants, and help them avoid over-reliance on automated tools that may be defeated by anti-forensics. We will present techniques for analyzing obfuscated JavaScript and VBA/VBS downloader scripts embedded in phishing email attachments. We will demystify malicious PowerShell being used for post-exploitation activities or how an adversary can try to regain a foothold via a PHP tiny webshell. This talk is for anyone on a blue team without a dedicated malware analyst, or anyone interested in malware analysis, but intimidated by all that hex.
CTF
PRIMARY CTF
The Primary Pittsburgh BSides CTF is designed to reflect real life scenarios faced by security professionals when deployed in the field. In this offense-only event, the individual's job is to penetrate several layers of an environment and collect flags for points along the way. Our CTF tech team consists of active security professionals with decades of experience in penetration testing. Their experience, expertise, and know how are leveraged to create a fun CTF that is technically challenging and realistic.
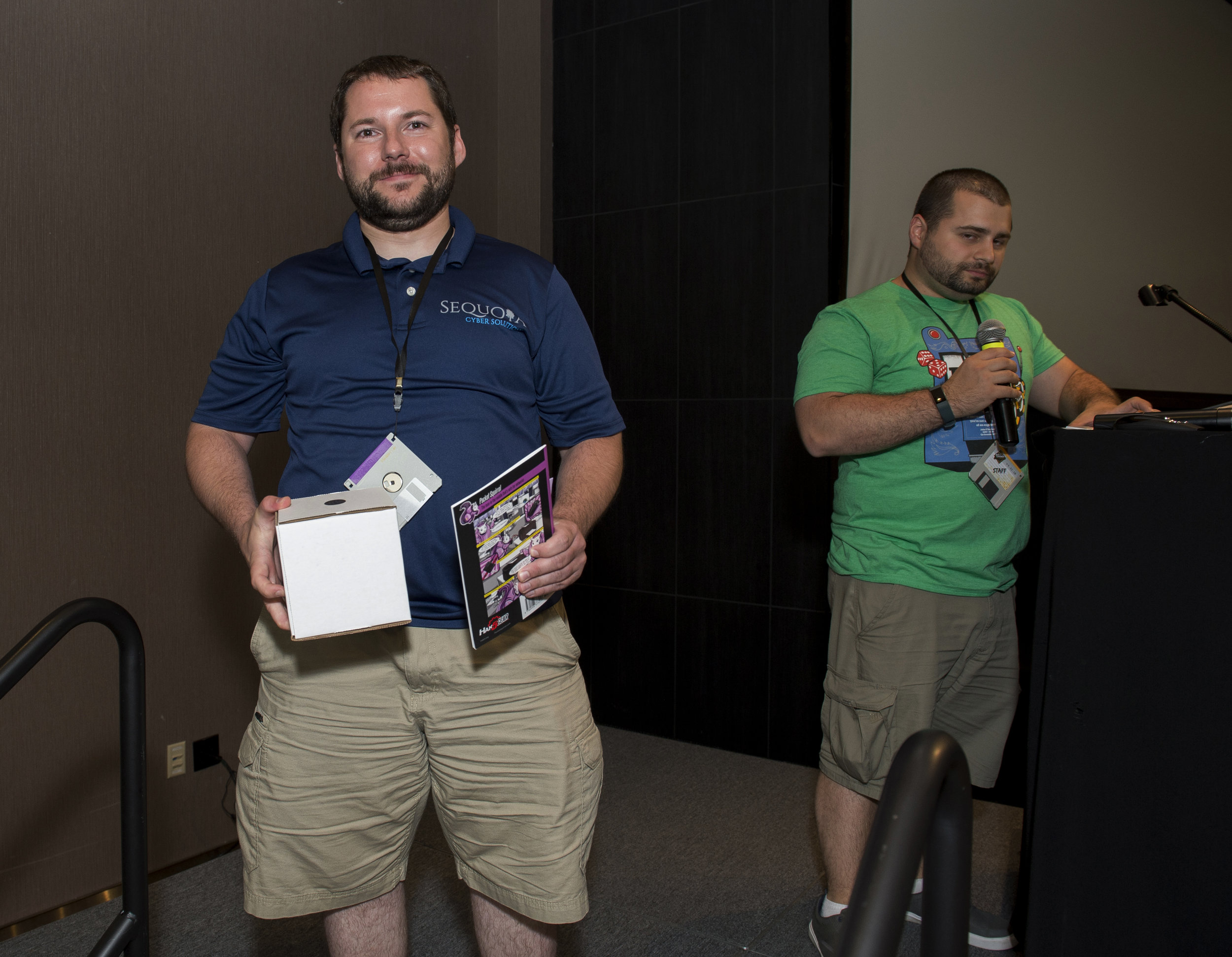
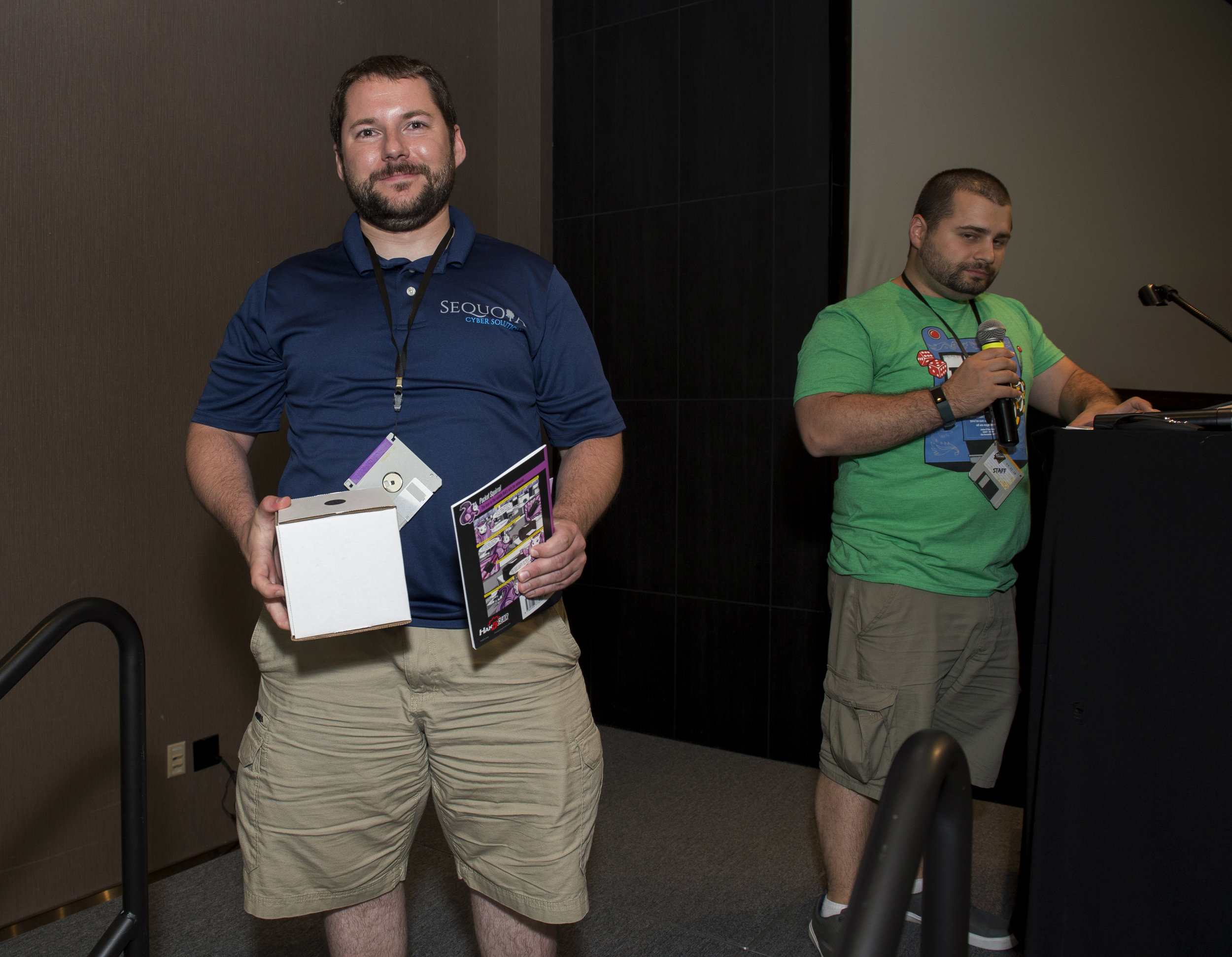
There will be prizes for the top 3 participants in the "Primary" CTF (Hak5 gear, NetWars subscriptions, challenge coins, and more!). In case of a tie for 1st, 2nd, or 3rd, the ranking will be determined by person taking least amount of time to capture the flags.
(MINI) WIRELESS CTF
Do you have what it takes to hack WiFi and Bluetooth?
The Wireless Village is holding a mini Wireless Capture the Flag (WCTF) at BSidesPGH.
TL;DR - twitter @wctf_us - website http://wctf.us - play with us
We cater to those who are new to radio communications as well as to those who have been playing for a long time. We are looking for the inexperienced player on up to the SIGINT secret squirrels to play this year. The WCTF can be completely done with a little knowledge, a pen tester’s determination, and $40 or $4000 worth of equipment, but the key is to read the clues and determine the goal of each step. In this special mini edition the focus will be on Wifi, bluetooth, and signal hunting.
Each WCTF begins with a presentation on How to WCTF. There will be clues everywhere, and we will provide periodic updates so make sure you pay attention to what’s happening at the WCTF desk, on twitter @wctf_us, the interwebz, etc. If you have a question - ASK, and we will determine if we will answer.
ABOUT US:
The Wireless Village is a group of experts in the areas of information security, WiFi, and radio communications with the common purpose to teach the exploration of these technologies. We focus on teaching classes on WiFi and Software Defined Radio, presenting guest speakers and panels, and providing the very best in Wireless Capture the Flag (WCTF) practice to promote learning.
POINT3 CTF
The Point3 Security ESCALATE CTF will put individuals to the test across multiple disciplines of the offensive and defensive security fields. The ESCALATE CTF consists of over 90 challenges that are worth various point values based on their difficulty. Will you try for multiple easier challenges to slowly build up your score or will you risk going big for one of the more difficult challenges that is worth a ton of points? The choice is yours!
The ESCALATE CTF has challenges focused on Networking, Programming, Reverse Engineering, Network Operations, Network Forensics, Linux Exploitation, Windows Exploitation, Web Exploitation, Implant Development, & Defensive Hunting.
The sign-up for the CTF will be at the Point3 table and the competition will run all day Friday. Whoever has the most points by the end of the day will be declared the winner! First place will receive a free 1 year subscription to ESCALATE ($3100 value) and 2nd & 3rd place winners will receive a free 3 month subscription to ESCALATE ($1450 value)!
About Point3:
We are a team of government-trained hackers hoping to stop the trend of “sophisticated attacker breaches enterprise, steals data”.
Each Point3 member has over 10 years of professional cyber security experience. Among their many security-related accomplishments, Point3 personnel have received a National Security Agency Director’s Team Award and have won hacking contests from DEFCON and Cyber Defense Competition events.
We built ESCALATE to train the next generation of cyber warriors. Instead of training today’s tools that address yesterday’s problems, we inspire apprentices to build their own solutions that solve tomorrow’s problems.
Sponsors
- Premier Sponsor
- TrustedSec
- Diamond Sponsor
- Ethical Intruder
- Platinum Sponsors
- AccessData
- Cadre & Tenable
- Carbon Black
- Cisco
- Crowdstrike
- ISM & Point3
- Optiv
- SecureWorks
- Security Risk Advisors
- Splunk
- Sumologic
- Gold Sponsors
- ISSA
- SANS
- Seiso
- Silver Sponsors
- Carnegie Mellon University Software Engineering Institute
- Dark Rhino
- Friends of BSidesPGH
- Association of Computing Machinery Digital Threats: Research and Practice
- Bit-x-Bit
- BrainBabe
- Infolock
- InfraGard Pittsburgh
- #RedChairPGH
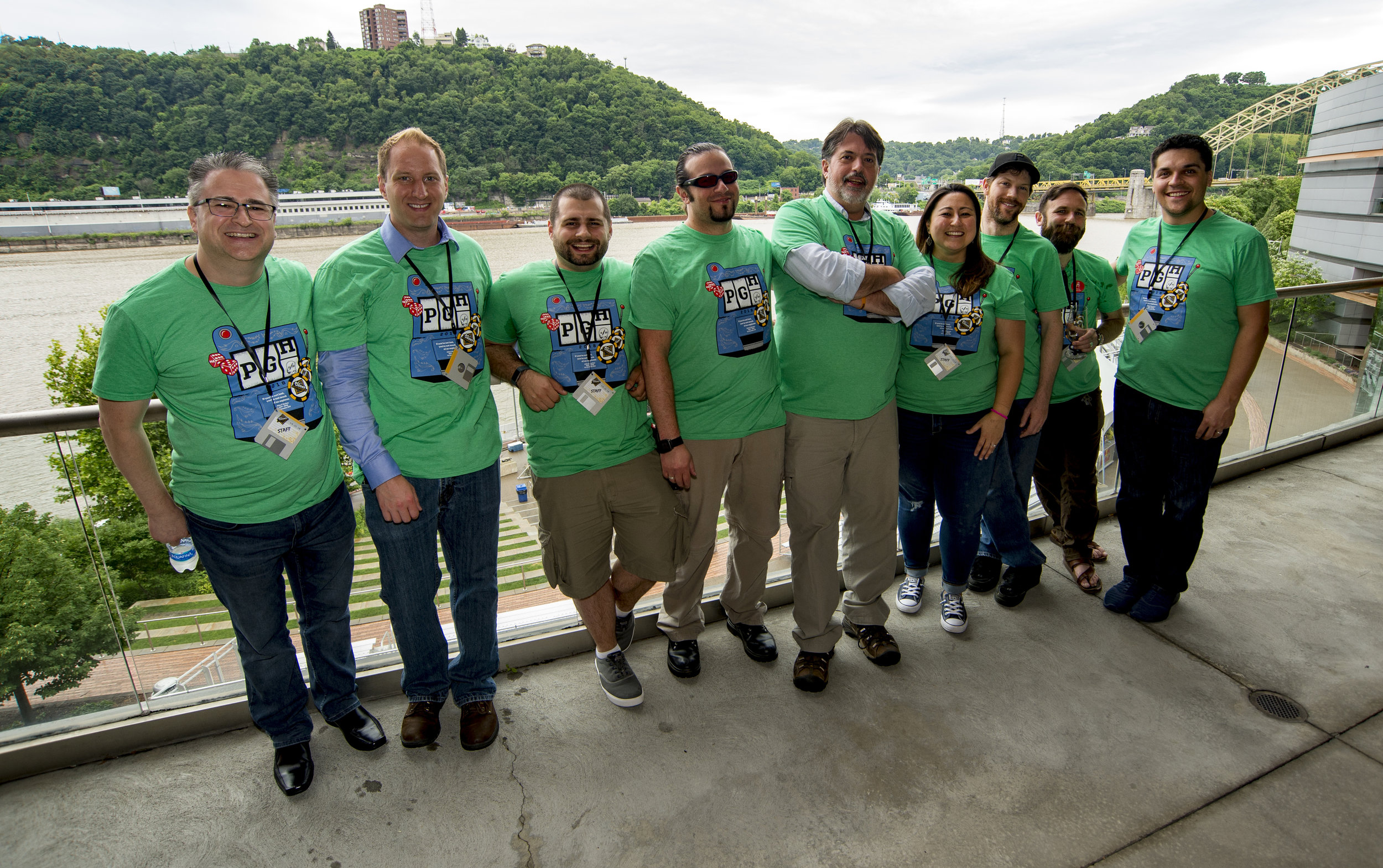
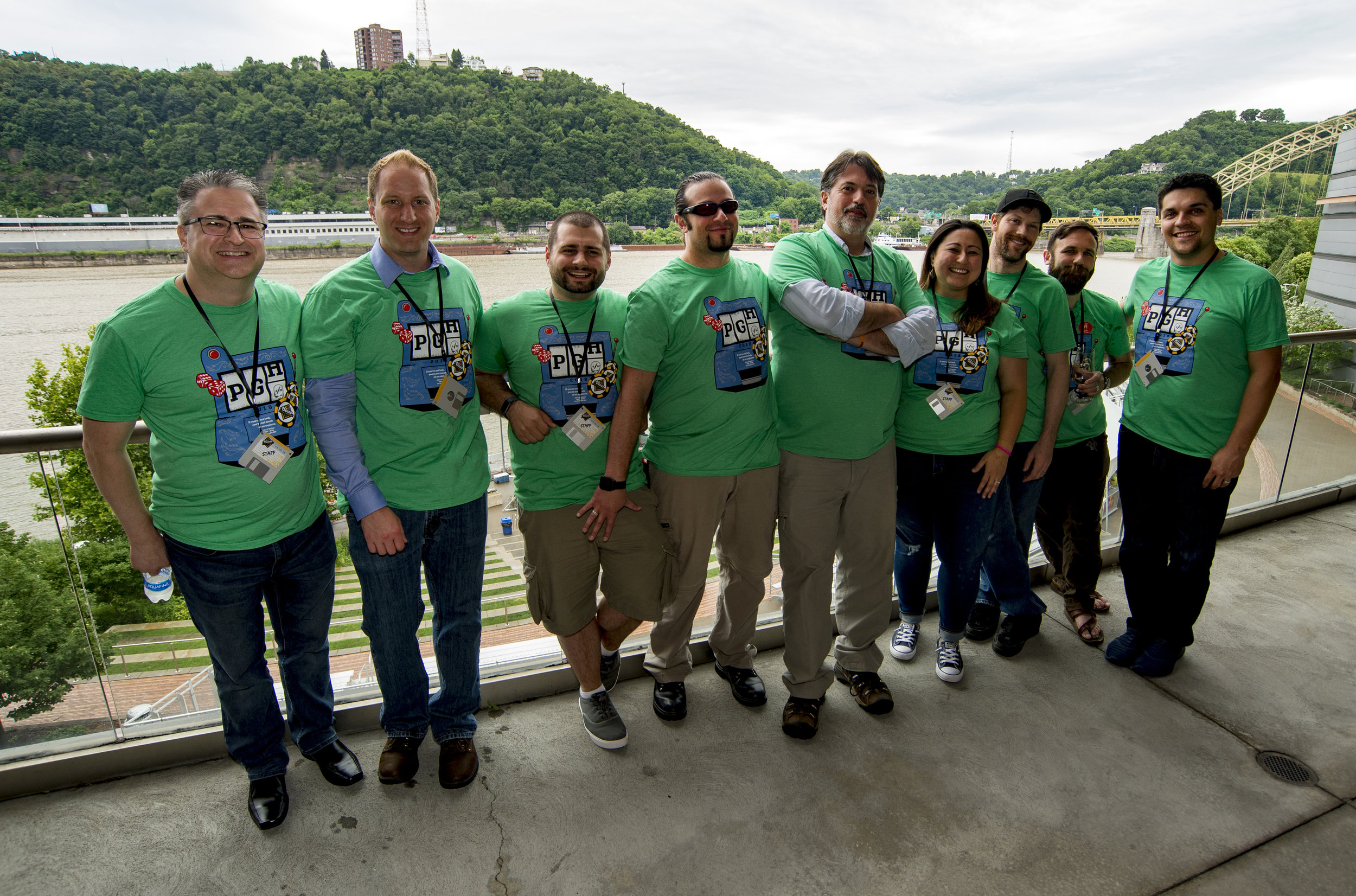
People
Joe Wynn @WynnJoe
Andy Johnson @PierogiPowered
Annie Howard @Einlace
Jon Zeolla @JonZeolla
John Kostuch @Kostuch
Brian Gray @BrianWGray
Eric Jenko @EricJenko
Zero_Chaos @Zero_ChaosX
Jonathan Baeckel